Column Level Security
PostgreSQL's Row Level Security (RLS) gives you granular control over who can access rows of data. However, it doesn't give you control over which columns they can access within rows. Sometimes you want to restrict access to specific columns in your database. Column Level Privileges allows you to do just that.
This is an advanced feature. We do not recommend using column-level privileges for most users. Instead, we recommend using RLS policies in combination with a dedicated table for handling user roles.
Restricted roles cannot use the wildcard operator (*) on the affected table. Instead of using SELECT * FROM <restricted_table>; or its API equivalent, you must specify the column names explicitly.
Policies at the row level
Policies in Row Level Security (RLS) are used to restrict access to rows in a table. Think of them like adding a WHERE clause to every query.
For example, let's assume you have a posts table with the following columns:
iduser_idtitlecontentcreated_atupdated_at
You can restrict updates to just the user who created it using RLS, with the following policy:
123create policy "Allow update for owners" on posts forupdate using ((select auth.uid()) = user_id);However, this gives the post owner full access to update the row, including all of the columns.
Privileges at the column level
To restrict access to columns, you can use Privileges.
There are two types of privileges in Postgres:
- table-level: Grants the privilege on all columns in the table.
- column-level Grants the privilege on a specific column in the table.
You can have both types of privileges on the same table. If you have both, and you revoke the column-level privilege, the table-level privilege will still be in effect.
By default, our table will have a table-level UPDATE privilege, which means that the authenticated role can update all the columns in the table.
123456789revokeupdate on table public.postsfrom authenticated;grantupdate (title, content) on table public.posts to authenticated;In the above example, we are revoking the table-level UPDATE privilege from the authenticated role and granting a column-level UPDATE privilege on just the title and content columns.
If we want to restrict access to updating the title column:
12345revokeupdate (title) on table public.postsfrom authenticated;This time, we are revoking the column-level UPDATE privilege of the title column from the authenticated role. We didn't need to revoke the table-level UPDATE privilege because it's already revoked.
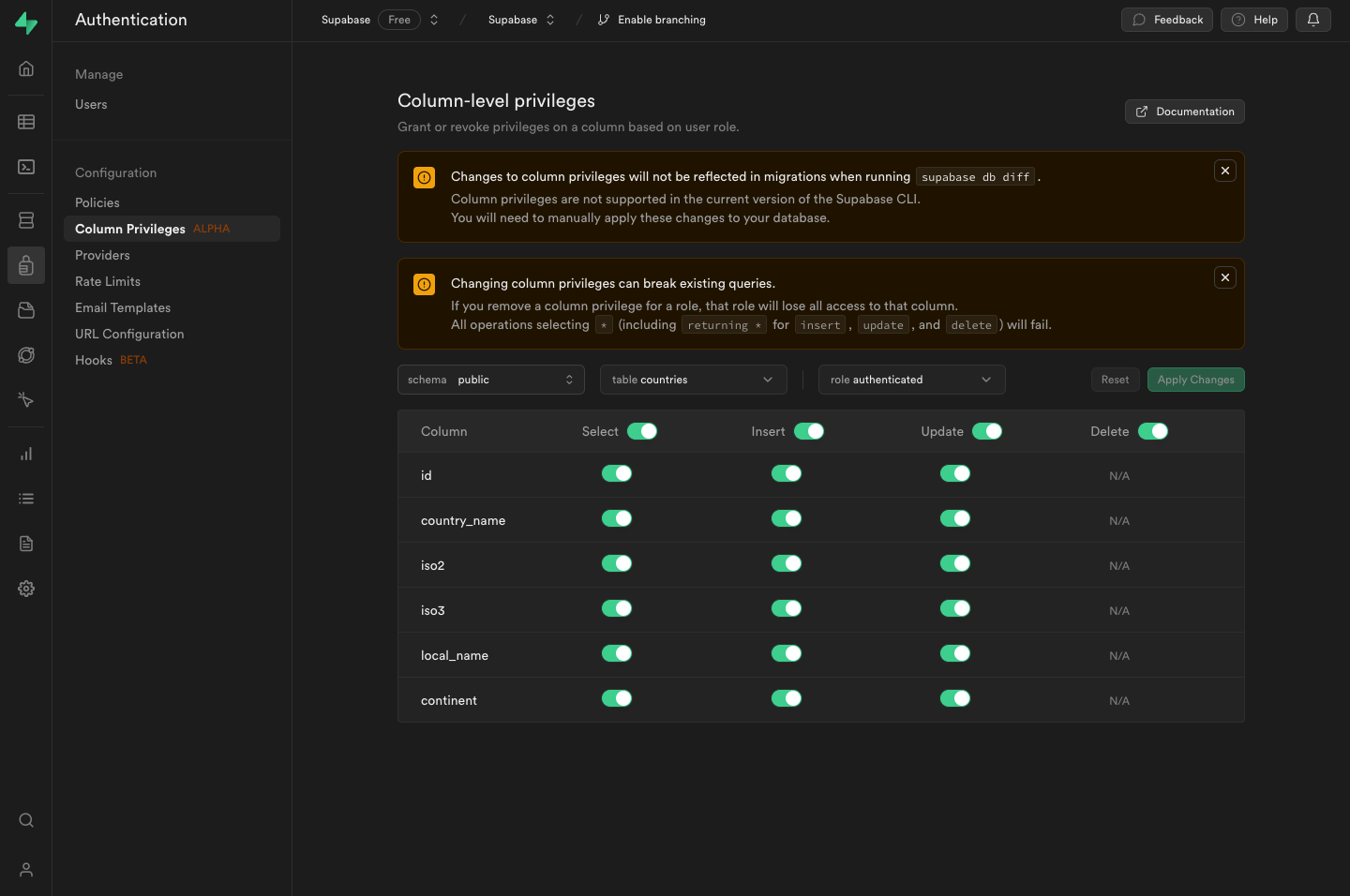
Manage column privileges in the Dashboard
Column-level privileges are a powerful tool, but they're also quite advanced and in many cases, not the best fit for common access control needs. For that reason, we've intentionally moved the UI for this feature under the Feature Preview section in the dashboard.
You can view and edit the privileges in the Supabase Studio.
Manage column privileges in migrations
While you can manage privileges directly from the Dashboard, as your project grows you may want to manage them in your migrations. Read about database migrations in the Local Development guide.
Create a migration file
To get started, generate a new migration to store the SQL needed to create your table along with row and column-level privileges.
1supabase migration new create_posts_tableAdd the SQL to your migration file
This creates a new migration: supabase/migrations/<timestamp> _create_posts_table.sql.
To that file, add the SQL to create this posts table with row and column-level privileges.
123456789101112131415161718192021create tableposts (id bigint primary key generated always as identity,user_id text,title text,content text,created_at timestamptz default now()updated_at timestamptz default now());-- Add row-level securitycreate policy "Allow update for owners" on posts forupdateusing ((select auth.uid()) = user_id);-- Add column-level securityrevokeupdate(title) on table public.postsfromauthenticated;Considerations when using column-level privileges
- If you turn off a column privilege you won't be able to use that column at all.
- All operations (insert, update, delete) as well as using
select *will fail.